Ah yes, beleive a state that is on trial in both the courts in The Hague (war crimes, crimes against humanity and genocide).
We sent aid and bombs. The bombs got through but not the aid. We are working on it.
/s
The guy was delivering food to a starving population. The occupation could have captured him since they have a military presence and control in the area.
and the MFA we all have
It's the government's pet religious authority. They will produce any opinion that the government wants. Is there a name for these kind of scholars in Islamic history?
Your field of study is not directly relevant here (unless you work to figure out the death toll, maybe). However scholars that do study genocide do now seem to agree that the killing of Palestinians by Israel is a genocide.
The last civil war didn't quite totally destroy the country. Let us try again.
The 40,000 killed statistic is reliable in that the killed persons name, identity number etc are reported to MoH officials and recorded by them, and the dead are seen by the officials. However the figure is a small subset of the actual number dead. 200,000 to 300,000 dead in Gaza in the past year is a conservative estimate.
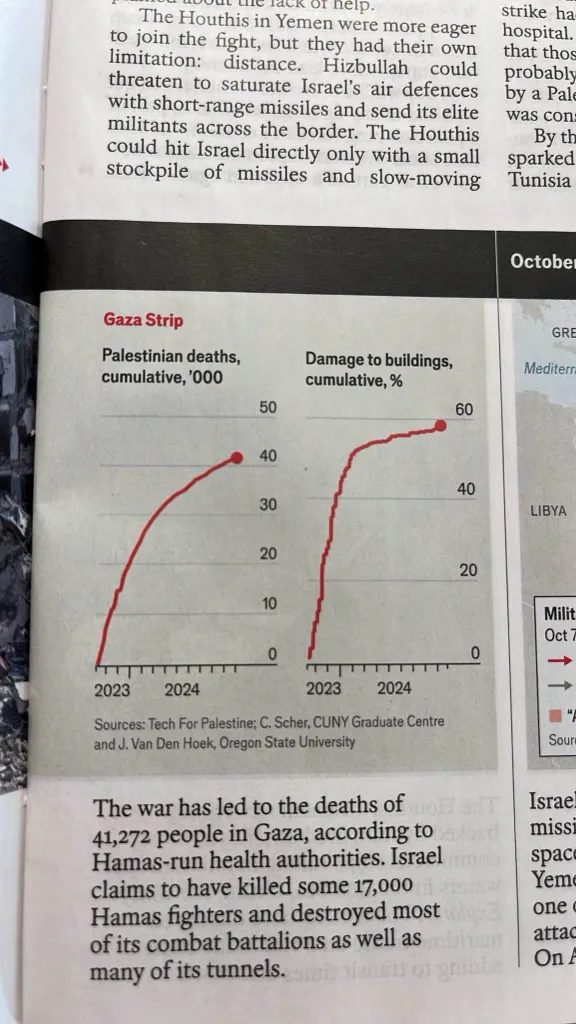
The Economist had a good (probably unintentional) illustration of this.
The killing according to the Gaza Ministry of Health statistics seems to be slowing down, but this is because the MoH is maintaining a very high bar for recording the deaths. The attacks on the population is continuing at what seems to be the same rate.
from: https://www.dropsitenews.com/p/how-gaza-health-ministry-counts-dead "The Ministry of Health is committed to registering only those who reach its hospitals or other emergency medical care facilities in the Gaza Strip. Consequently, the number of martyrs announced by the ministry does not necessarily represent the total number of casualties but only those that have been officially documented."
Given that state of the hospitals is dire (they have all been bombed and attacked), the slow down in recording of deaths correlates with and is due to the destruction of the MoH and general civilian infrastructure. The reduction in rate of killing recorded does not align with the rate of actual killing.
Also, have you ever wondered why South Africa of all countries brought the case to the ICJ? Probably because they are deeply offended by the Israeli apartheid and they are even more against genocide?
Do you think it has anything to do with the fact that they entertained Hamas leaders as visiting dignitaries a month before they submitted the case? Um, yes. Why would they not do this?
Ah, you classify Hamas as a terrorist organisation.... Since South Africa regards Hamas to be a resistance movement (and this is the position of most of the world), coordinating with them would be sensible.





A trail does review evidence whereas here we just had a summary execution.
Your link to them UN press release says this:
"OIOS was not able to independently authenticate information used by Israel to support the allegations."