this post was submitted on 28 Apr 2024
32 points (79.6% liked)
Security
5005 readers
1 users here now
Confidentiality Integrity Availability
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
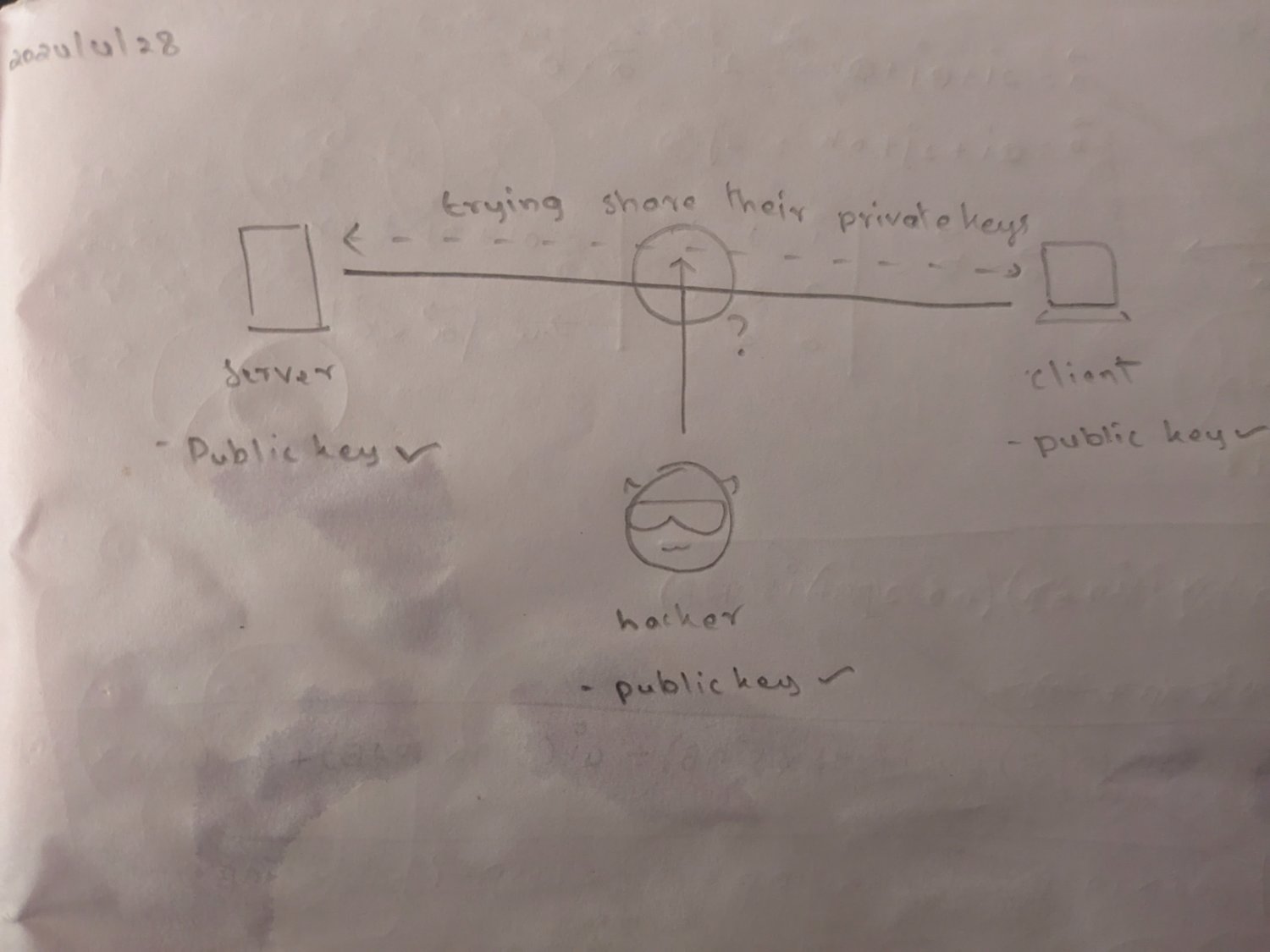
You've missed a key detail in how asymmetric encryption works:
I didn't believe this is true... In public/private key crypto there is no such thing as "private" and "public". They're just a key pair. You choose to make one public by sharing it and the other private by not sharing it.
It depends on the cryptosystem. The private and public halves of the pair are often not symmetrical and often have overlap.
The parent is likely confused because in most situations the "private key file" will also contain all of the public key. Whether by necessity or for convenience.